QR codes have become ubiquitous thanks to the ease with which smartphones can scan them, but users have no reliable way to detect tampering by eye. This creates a significant security risk: a QR code can be modified to point to a malicious destination while looking identical to the legitimate one, and the alteration may go unnoticed for a long time.
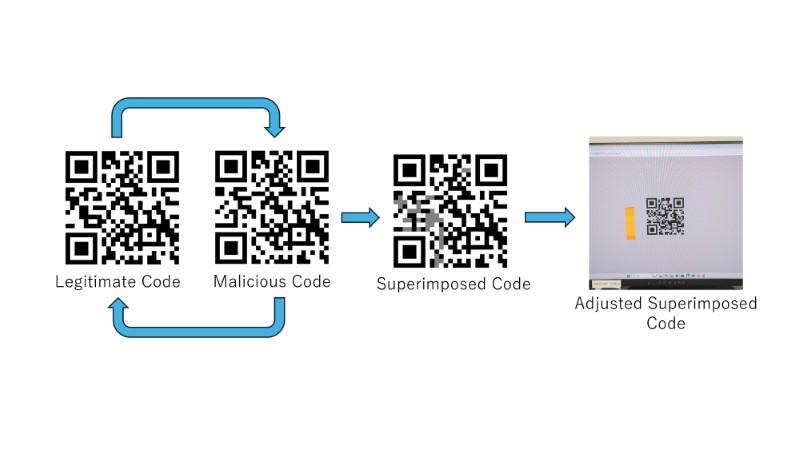
We propose a new attack method that exploits high refresh rate monitors capable of driving at 120Hz or higher. The display rapidly alternates between a legitimate and a malicious QR code, so a human observer perceives only a single, static-looking code, while a camera scanning the display will probabilistically capture one of the two. Compared to existing visual-disguise techniques, this approach is considerably harder to detect by eye and affords the attacker far greater freedom in crafting the malicious payload.
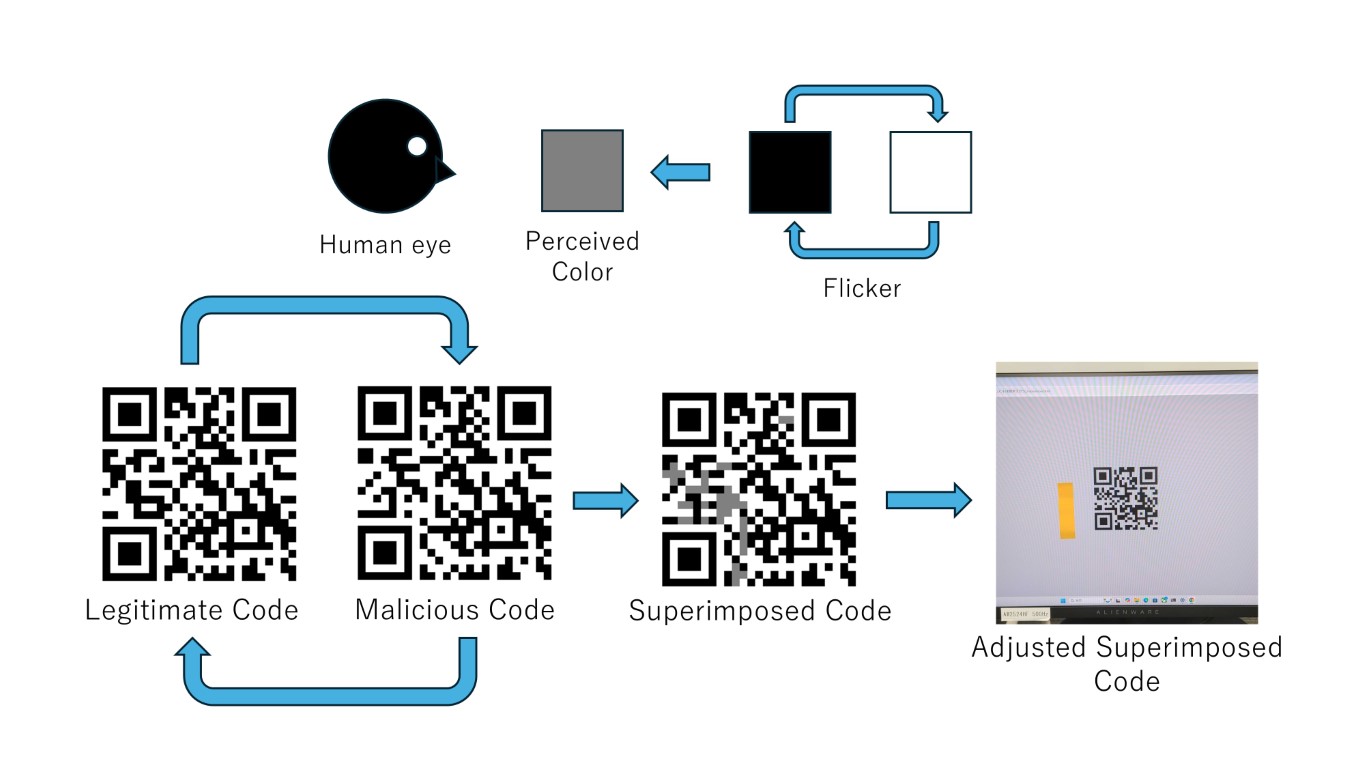
Our evaluation experiments demonstrated that malicious data with minimal modifications from legitimate codes could evade detection in approximately 80% of cases. Furthermore, we confirmed that the probability of capturing malicious data can be controlled by adjusting the alternating display patterns.
On LCD displays, the technique imposes constraints on what content can be tampered with. Switching to LED displays eliminates these constraints, enabling significantly more flexible manipulation of the embedded data.
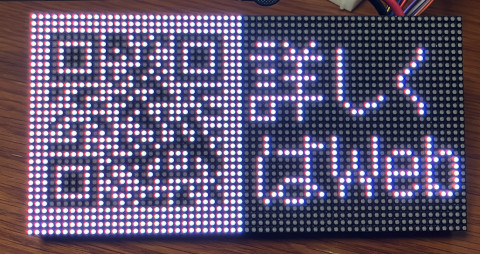
A tampered QR code displayed on an LED display